How do scammers get so much info about you
Your personal data is currency. Criminals use it to pass security checks, unlock accounts, and convincingly act as you long enough to drain money, open credit, or lure your friends, family, or colleagues into new scams. In the U.S., the FTC logged over 1.1 million identity-theft reports in 2024; in Australia, official data shows identity crime and scam exposure remain widespread even as overall reported scam losses fell in 2024.
What criminals do with your data (and why it pays)
- Impersonate you to your bank, telco, or tax authority (passing routine security questions).
- Take over accounts (email, banking, crypto, social) then reset passwords everywhere via “forgot password.”
- Trick your contacts with believable messages sent from your real accounts.
- Steal money or benefits (refund fraud, government payments, chargeback abuse).
- Open credit in your name (loans, buy-now-pay-later, devices), then disappear.
- Build “synthetic identities” by mixing your real details with fakes to create new, credit-worthy personas.
- Resell your profile (so-called “fullz”) on criminal marketplaces for repeat monetisation.
The highest-value pieces of your identity
- Government IDs: Driver’s licence, passport, Medicare card (AU), Social Security number (US), Tax File Number (AU). These unlock bank/telco changes and new-account applications. Australia now operates a Credential Protection Register to help “lock down” compromised IDs used in digital verification checks.
- Account access primitives: Email address + phone number + date of birth (plus any reused passwords).
- Financial rails: Card numbers, BSB/routing and account numbers, crypto wallet addresses, and 2FA methods.
In 2024, Australians reported over $93 million lost due to identity theft-related scams (Scamwatch), while the FTC in the US recorded over 1.1 million identity theft complaints.
Knowing how scammers get this information is the first step to protecting it.
1. Data Breaches and Hacks
This is the most common source of leaked information. When companies are hacked, scammers can buy or download:
- Names and emails
- Phone numbers
- Addresses
- Passwords
- Payment info
Example: The Optus breach in Australia (2022) exposed sensitive data of millions of users. Years later, that same data is still circulating.
US Example: In 2024, a major retail chain was hacked, leaking 15 million user emails and addresses, many of which were later used in phishing scams.
How they use it:
- Craft personalised phishing emails
- Reset your passwords on other platforms
- Sell your info on the dark web
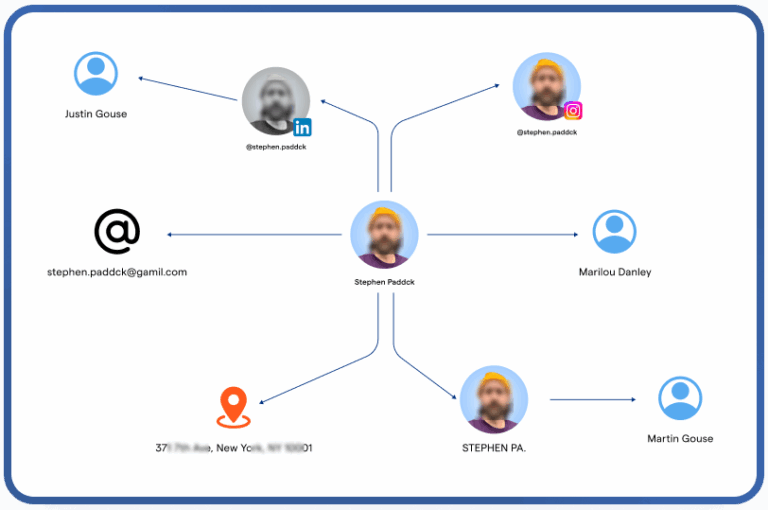
2. Public Records & OSINT
Open-source intelligence (OSINT) means scammers gather data from publicly available sources, including:
- Social media profiles
- WHOIS domain records
- Government records (e.g., ASIC, SEC)
- Forums, blogs, and event pages
Example: Someone finds your birthday on Facebook, your work email on LinkedIn, and your phone number on your business website. They combine all of that to impersonate you.
They might:
- Guess your security questions
- Impersonate you to your employer or bank
- Use your identity in romance or job scams
3. Mobile App Permissions
Apps that request access to contacts, messages, location, or files can leak more data than you think. Even simple games or flashlight apps can:
- Sell data to third parties
- Leak info via SDKs (Software Development Kits)
- Be embedded with malware
Tip: Check your phone’s privacy settings and only install apps from trusted developers.
4. Phishing and Social Engineering
Phishing tricks you into giving information directly. This includes:
- Fake emails or SMS claiming to be from your bank, telco, or ATO/IRS
- Calls asking you to “verify” details
- Links to fake websites asking for logins
Real Case (Australia, 2024): Victims received SMS messages claiming to be from the myGov portal, asking them to log in and confirm details. The link went to a spoofed site that stole login credentials.
US Variation: IRS impersonation calls ramp up during tax season victims are told they owe money and must verify their info.
5. Data Brokers and People Search Sites
There are companies that collect and sell your information legally. They scrape:
- Shopping history
- Social media habits
- Address changes
- Public database records
Then, they sell it to advertisers or worse, it leaks or is scraped again by scammers.
Popular data broker sites: Spokeo, BeenVerified, Whitepages (US); IDWise, Equifax (AU).
6. Malware and Spyware
Scammers can infect your devices through:
- Fake software downloads
- Infected email attachments
- Malicious links in ads or DMs
Once installed, malware can:
- Record keystrokes (keyloggers)
- Steal stored passwords
- Access files and webcam
- Track your browsing history
Tip: Install antivirus software and avoid downloading from unofficial websites.
7. Scam Websites and Fake Forms
Many scammers create fake e-commerce sites or forms to collect your data. Common examples:
- Fake giveaways asking for name and number
- Counterfeit shops asking for credit card details
- Free downloads that require email and DOB
If the site looks shady or the deal seems too good to be true it probably is.
8. Parcel and Delivery Scams
In 2025, delivery scams are surging. You might get a message:
“Your package is delayed. Click here to update your address.”
These links often:
- Mimic AusPost or USPS
- Ask for address, email, and credit card
- Install malware
They use your info later for identity theft or phishing.
9. Social Media Quizzes and Games
Those viral quizzes like “What’s your elf name?” often ask for:
- Birth month
- Pet’s name
- Favorite teacher
These answers can be used to guess your passwords or answer security questions.
How to Protect Your Info
- Use strong, unique passwords for each account
- Turn on 2FA (authenticator apps > SMS)
- Be cautious of what you post publicly
- Limit app permissions
- Don’t reuse passwords
- Use antivirus and secure Wi-Fi
- Regularly check HaveIBeenPwned for breaches
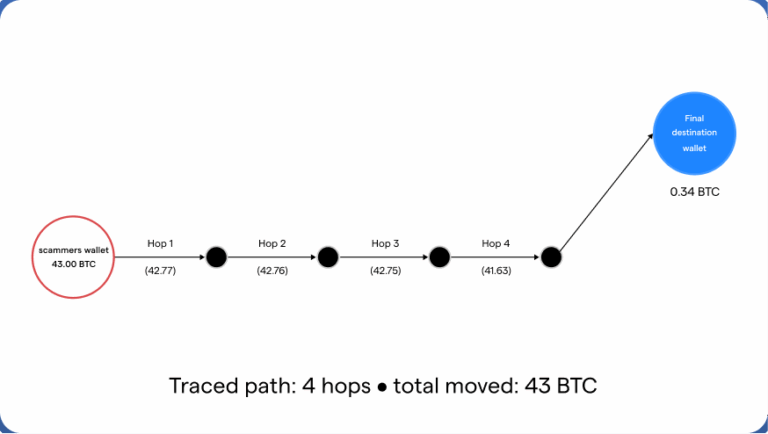
How CypherGuard Helps
If your data is leaked, CypherGuard can:
- Trace how your data was obtained
- Investigate phishing and social engineering attempts
- Identify malicious domains or scripts
- Document forensic evidence for banks and legal action
- Monitor for impersonation scams or financial fraud
Our cyber intelligence tools help you reclaim control fast before more damage is done.
Reporting Leaks or Identity Theft
Australia:
- Scamwatch.gov.au – Report scams
- IDCARE.org – Identity theft support
- Office of the Australian Information Commissioner – Data privacy breaches
United States:
- IdentityTheft.gov – Report and recover
- FTC.gov/complaint – General fraud reporting
- Equifax, Experian, TransUnion – Freeze your credit
FAQ
Q: I never shared my info. How did scammers get it?
A: Likely through a data breach or a service that sold your info. Breaches can happen silently.
Q: Can social media really put me at risk?
A: Yes. Public birthdays, job titles, and photos can help scammers impersonate or target you.
Q: Are quizzes and giveaways on Facebook safe?
A: Many are designed to harvest your info. Avoid ones that ask for personal details.
Q: Is my data sold legally?
A: Yes, in some cases. Data brokers collect and resell info legally though it often ends up misused.
Q: How do I know if I’ve been breached?
A: Use HaveIBeenPwned.com to check email or phone leaks.